Whoa! The first time I clicked “connect” on a Solana NFT marketplace I felt my stomach drop. I mean, really? I was giving a little piece of my browser permission to move things. My instinct said: slow down. Initially I thought browser wallets were all the same, plug-and-play conveniences, but then I noticed subtle differences that mattered for security and usability.
Okay, so check this out—wallet extensions are the most common on-ramps to Solana dapps. They sit right in your browser toolbar. In one click you can sign a trade, list an NFT, or approve a token swap. That convenience is huge. It also makes them a high-value target for phishing and malicious sites.
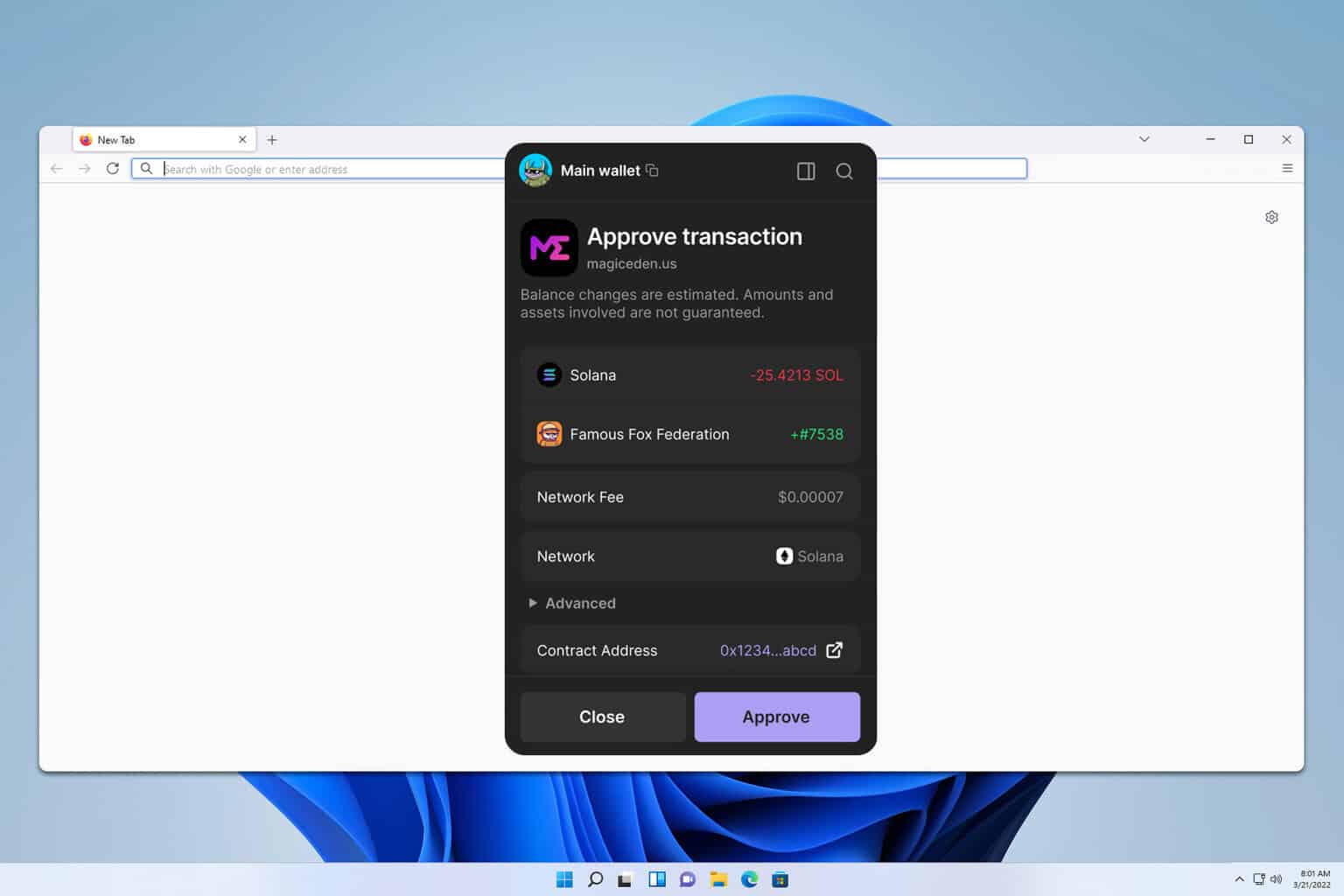
Here’s the thing. Some wallets are lightweight and fast. Others pile on features (multi-account, hardware fallback, deep NFT views) and feel clunky. On one hand speed matters; on the other, clarity and control matter more when you’re moving NFTs worth real money. I’m biased, but the UI that makes signing transactions explicit and readable is a must. Something felt off about buttons labeled only “approve” with no context—very very important to avoid that.
Short aside: I once approved a transaction that I thought was a listing fee. It wasn’t. Oof. Lesson learned. Hmm… let me rephrase that—what saved me was quick reaction and a hardware wallet fallback, which stopped a larger problem. So yeah, hardware integration is a huge plus.
How to pick a Solana browser wallet (practical checklist)
Seriously? There are more wallets than you think. Focus on these practical signals: open-source code, active audits, meaningful bug bounty, good UX for NFTs, and straightforward permission prompts. Also check whether a wallet offers clear token/NFT metadata and transaction memos—those little details reduce mistakes. I installed phantom to test how a mainstream option handled NFT approvals and found its gallery view helpful (oh, and by the way… the onboarding is smooth).
Short version: prefer wallets that explain each permission. Medium version: wallets should show who is requesting access, what exactly they can do, and how long that access persists. Longer thought: because browser extensions sit in a shared environment, they must compartmentalize permissions robustly, and that architecture is what separates a comfy user experience from a risky one, especially when NFTs are involved—metadata and royalties get messy.
I’ll be honest: the extension model has tradeoffs. Easier to use than hardware-only setups, but more exposed. On the flip side, for frequent NFT collectors and traders the speed and UX wins out. My working rule: keep a small hot wallet for active trades and a secure cold wallet for high-value assets. Initially I thought a single wallet could do it all, but real usage showed me otherwise.
Security habits that help: keep your browser updated, use separate profiles for wallets, and revoke dapp approvals you no longer trust (many wallets and explorers let you do this). Also avoid clicking links from DMs—phishing is the low-hanging fruit for attackers.
There’s also the question of NFT handling. Some wallets display attributes and art inline, which helps you confirm what you’re signing. Others only show token IDs and program addresses, leaving you to guess. That ambiguity is what bugs me about a few popular wallets—it’s easy to accidentally sign the wrong asset when the UI hides crucial context.
Hmm… on policy and privacy: some extensions collect telemetry or analytics by default. That might be fine for benign usage stats, but I prefer opt-in analytics. My instinct said to check permissions and privacy policies before trusting an extension with my NFTs.
Longer analytical point: browser extensions are code that runs in your browser context; they share the rendering surface with web apps. This shared context creates subtle attack vectors—content scripts can be intercepted, and UI overlays can be mimicked by malicious pages. Because of that, wallet developers who implement transaction staging and require explicit user confirmation for each signing step are doing the heavy lifting for you. Initially I thought a single confirmation popup was enough, but then I saw examples where an attacker could spoof details. Actually, wait—let me rephrase that: one popup is fine only when the wallet’s UX makes the context and purpose crystal clear.
Practical tips for NFT collectors: keep collections you actively trade in your browser wallet and move legacy or high-value pieces to cold storage. Back up seed phrases the old-fashioned way—paper or hardware backups—and test recovery procedures. Don’t screenshot seeds or store them in cloud storage. It’s tempting, and I almost did it once…
Common questions about Solana wallet extensions
Q: Can I use a browser extension for high-value NFTs?
A: Short answer: cautiously. Medium answer: for daily interactions it’s fine, but for very valuable NFTs use hardware-secured wallets or move assets to a cold wallet. Longer thought: consider using a multisig or dedicated vault if you hold collectibles with significant financial or sentimental value; those setups add friction but greatly reduce single-point compromise risk.
Q: What should I watch for during a transaction?
Watch who is requesting approval, the program IDs, the exact token and quantity, and any unusual memo or destination addresses. Also check for repeated or chained approvals—if a dapp asks to “approve unlimited spending” think twice. My gut said unlimited approvals are often unnecessary… often unnecessary.







